With the Covid-19 pandemic, many people are forced to work from home. Unfortunately, they are using home technology and networks, which may not be the best suited for work purposes. For instance, their wireless networks may have dead spots and be slow. Many people have not heard of a relatively new technology called wireless mesh networks.
In this article, we explain what mesh networks are and how they can improve both home and office wireless network performance.
Mesh Networks Explained
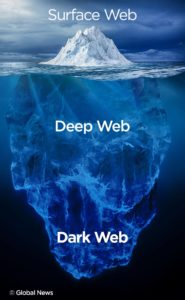
In the traditional home or office network, you have a modem and router (or combo unit), which sends a wireless signal to all devices. In some cases, you may also install a wireless extender, which extends the wireless signal further from the router.
One issue with this network is that the router and extender transmit networks with different names and passwords. As you move around, you have to manually switch from one network to another on your phone or computer. Also, there can be Internet speed and performance issues when using an extender. Normally, the wireless extender provides a network which has significantly slower speeds than the router’s network.
Mesh Networks consist of what are called nodes or satellites. Usually, one of these nodes works like a router, while the other nodes connect to this router or themselves. This means that you can install many different nodes throughout your home or office, if you like.
Since they are all part of the same network, the wireless performance should not drop significantly from one satellite to another. Most importantly, they send out a wireless signal with the same network name and password. Therefore, you don’t have to manually connect to one network as you get closer to it. Your phone or computer will always remain connected.
Mesh Networks Advantages
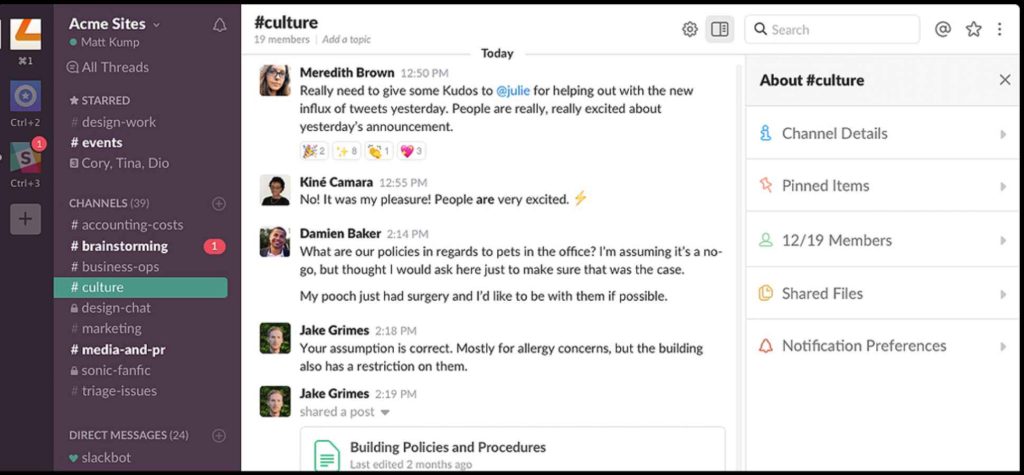
Easier to Use
One advantage of these networks is their ease of use. At your home or office, you have one mesh network. As you move around the network, you computer or other device will automatically stay connected to the network. The mesh network will continuously be looking to connect you to the optimal wireless node. Even when connected to one node, it will find the optimal connection to that node.
With traditional wireless router and wireless extender networks, your device will stay connected as long as it can to the wireless unit it is connected to. As you move to one side of your home, you have to manually switch to the nearest wireless device.
Better Performance
Generally, mesh networks will provide better network performance than traditional router and wireless extender networks. Your computer, smart phone or tablet will get a strong wireless signal with better speeds throughout your house or office. On the other hand, extenders normally transmit wireless signals which have noticeably slower Internet speeds than the main router.
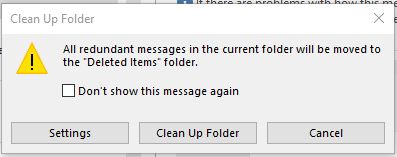
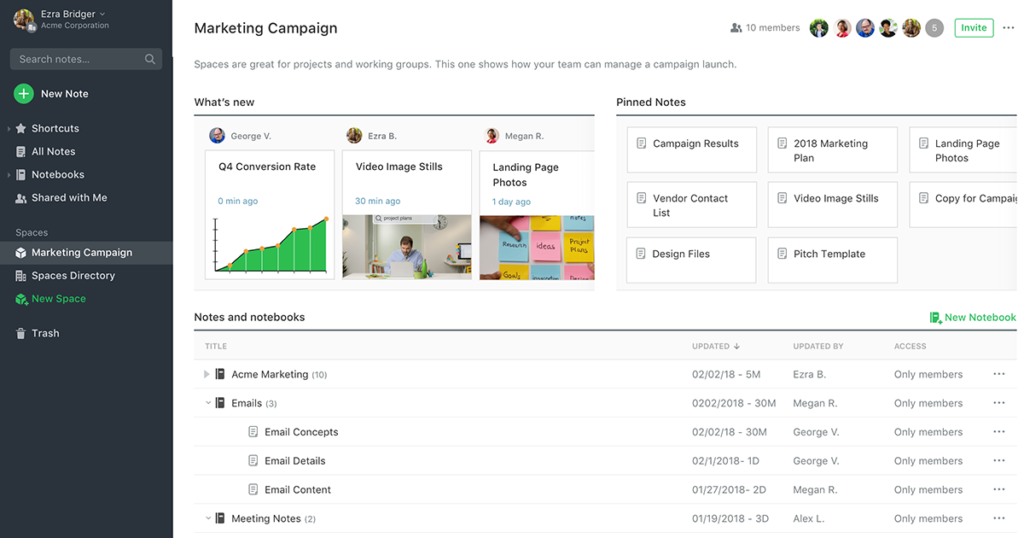
Easier Installation & Management
Usually, you can install a smart phone app to set up and manage your wireless mesh network. From this app, you can add new nodes, change the network security settings, enable a guest network, and block users. Normally, you can add new wireless nodes by clicking on an option in the app and then just plugging them in.
On the other hand, with a traditional router and extenders you usually have to set up each one separately on a computer or an app. Normally, you have to spend much more time installing and configuring the extenders.
When your home or business is hit by a power outage, a mesh network should automatically start working, once power is restored. Instead, a traditional network may not start working right away. You might have to reconnect wireless devices (i.e., router, extenders, etc.) one by one. This can take up a lot of time and energy.
Mesh Networks Disadvantages
The main disadvantage of mesh networks is their cost. Because you usually have to buy a 3 pack of mesh units, the cost is more than a typical router and extender. An Eero 3 pack is relatively inexpensive at about $175. A Nest Wi-Fi 3 pack of a router and two nodes costs about $349. The Netgear Orbi AC2200 pack has a similar price.
For individuals who live in a small apartment or a single floor house, a wireless mesh system may be overkill. A router should provide sufficient wireless coverage. These individuals could always add an inexpensive extender to strengthen the Wi-Fi signal throughout their place.
If you have any questions need assistance with your home or office network, please feel free to visit Nucleus’s Contact Us page.
References:
1 Tomsguide.com “What is a mesh Wi-Fi router and do you need one?” Link to Site
2 PCWorld.com “Wireless mesh networks: Everything you need to know” Link to Site
3 Support.Google.com “What is a mesh network” Link to Site
4 PCMag.com “The Best Wi-Fi Mesh Network Systems for 2020” Link to Site